Digital standards that rule the way the data is handled by a company are required measures that every company should follow. Although they must be implemented from a legal point of view, organizations are also able to apply these guidelines voluntarily to build a comprehensive defense against cyberattacks. This is called an Information Security Framework.
What is an Information Security Framework?
 An Information Security Framework is a set of documents, guidelines, standards, and requirements that define the policies, procedures, and processes in which your organization relies on. Even more, it shows clearly to all departments, in and out of your company, how your business manages information, services, and systems.
An Information Security Framework is a set of documents, guidelines, standards, and requirements that define the policies, procedures, and processes in which your organization relies on. Even more, it shows clearly to all departments, in and out of your company, how your business manages information, services, and systems.
Why is an Information Security Framework important?
The importance of an Information Security Framework relies upon the way it helps IT and security leaders to manage their organization cyber-risks in a more appropriate way. It also shows them the procedure to follow once an urgent or emergency situation arises.
Standards and guidelines you have to keep in mind to build an Information Security Framework
Before developing your company’s own Information Security Framework, it’s quite important that you get to know – or read again – some of the most frequented cybersecurity standards and guidelines nowadays.
ISO standards
 The International Organization for Standardization (ISO) created the ISO 27001 and 27701 guidelines, alongside the International Electrotechnical Commission. Let’s see what they are about and how they can help you develop your organization’s information security framework.
The International Organization for Standardization (ISO) created the ISO 27001 and 27701 guidelines, alongside the International Electrotechnical Commission. Let’s see what they are about and how they can help you develop your organization’s information security framework.
ISO 27001 – Information Security Management Systems
This one focuses on a risk-based approach to information security. ISO 27001 involves categories such a written security policy, HR security, asset management, access control, cryptography, physical and environmental security, incident management, business continuity management, and compliance with government regulations.
ISO 27701 – Information Privacy Management
Aimed at data privacy, these standards oblige data processors or controllers to prioritize the protection of personally identifiable information (PII) in every information security risk assessment.
CIS Benchmarks
As one of the most recognized cybersecurity organizations, the Center for Internet Security (CIS) offers detailed practice solutions for companies. These extensive but important documents help businesses secure their IT systems and data against cyber-attacks.
If you’re looking forward to building your company’s information security framework, there’s no doubt the CIS can be helpful for you. Especially through its library of Benchmarks, in which you must find the docs most related to your context and spend time poring over them.
Official standards
Industry and government standards are a must for businesses that are looking to develop their information security program. If your company falls into their area, and you don’t include the proper guidelines in your framework, they might apply heavy penalties on you. Here we leave you the most important policies you should take care of.
HIPAA
If your company handles personal health information such as employee data, then you must follow the Health Insurance Portability and Accountability Act’s (HIPAA) security guidelines. Although it doesn’t point out the exact practices or tools that must be used, HIPAA applies penalties of up to $1.5 million for not following its standards.
PCI DSS
On the other hand, your organization should include some type of payment through debit or credit card, then you must take a look at the Payment Card Industry Data Security Standards (PCI DSS) guidelines. The PCI DSS was created by Visa, MasterCard, and American Express. It requires companies to rely on strong firewall configurations and encryption.
NIST
The National Institute of Standards and Technology (NIST) provides a solid digital security foundation for any business owner who’s keen on getting a lucrative federal contract for his US-based company.
Specifically, NIST’s Cybersecurity Framework is a valuable resource in terms of identifying cybersecurity risks. Also for searching and detecting anomalous network activity, and enacting immediate response and containment efforts in breaches’ wake and data recovery.
DISA
The Defense Information Systems Agency’s (DISA) Security Technical Implementation Guides are a must in Defense Departments. However, they have a special feature: they’re updated quite more frequently than any other cybersecurity protocol. This makes them a fresh source of information for anyone who wants to develop their company’s information security framework.
GDPR
The General Data Protection Regulation (GDPR) protects individuals regarding the processing and free movement of personal data. It was first implemented in 2018. By now, every organization that collects EU residents’ personal data must follow this guideline.
How to build the ideal Information Security Framework for your company
Right now there are hundreds of information security framework possibilities in existence today. Follow these steps to develop your own infosec protocol according to your company’s cybersecurity needs.
Step 1: Get to know what’s on your network
The very first thing you have to do is to get a full access view of your company’s assets. In this case, a vulnerability assessment or vulnerability management solution can be quite helpful. Remember, your goal here is to know everything that’s on your network so you can secure it all.
Step 2: Follow the right guidelines
Next, you must understand the legally appropriate standards that fit in your organization’s ongoing. But even more, you can consider other guidelines that could bring valuable protection to your company.
Step 3: Test your cybersecurity settings
Then use vulnerability scanning, penetration testing, and threat modeling to examine your security backgrounds. This will get you an idea of how damaging attacks would be handled under different configurations, of course.
Step 4: Help yourself with the proper tool
Finally, you’ll want to build more protection around your company for sure. That’s exactly the point in which a cybersecurity tool can help. For example, Tenable’s Nessus is the perfect complement to any information security framework.
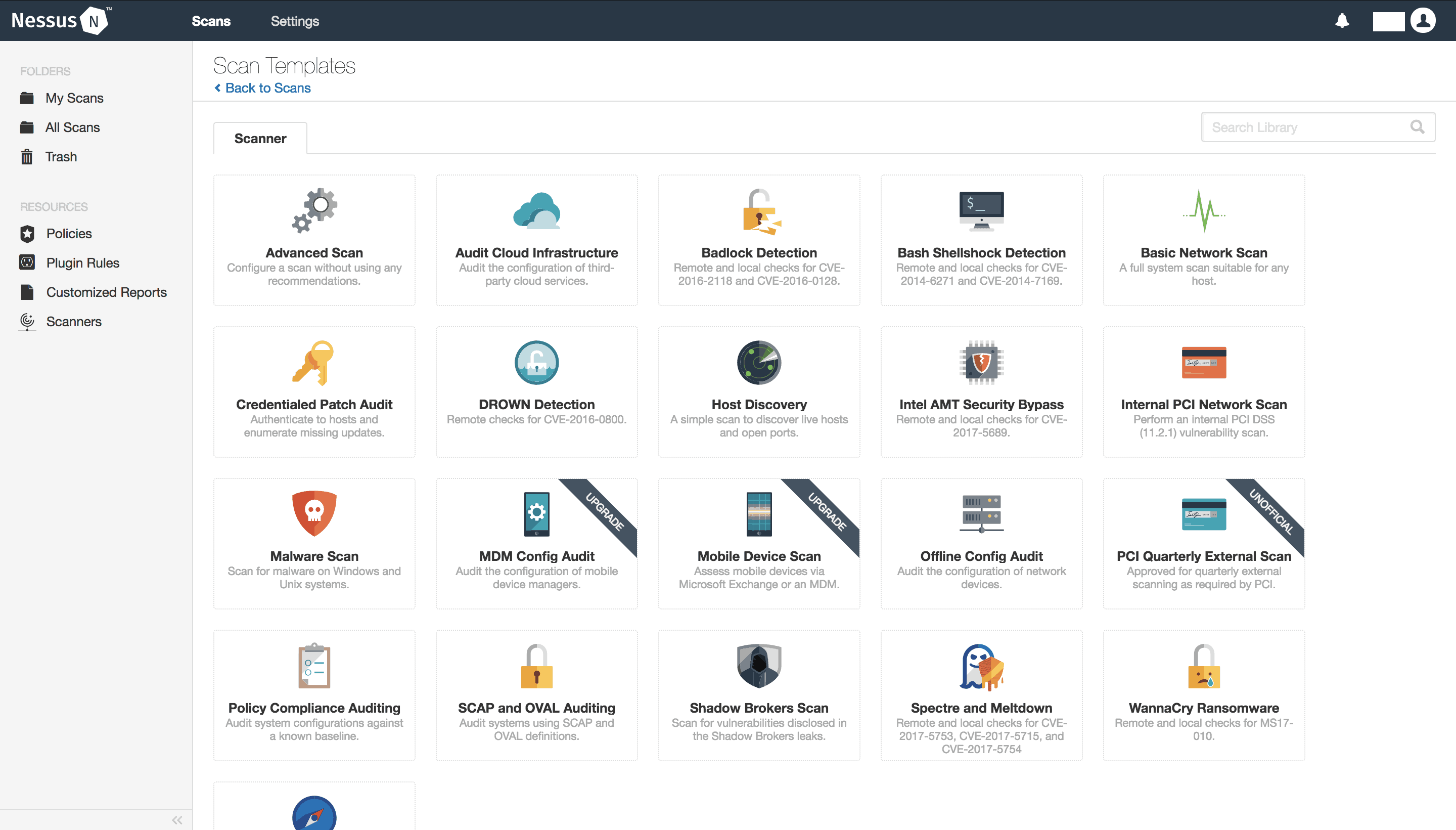
Besides, other software such as Tenable.sc and Tenable.io offer solutions to help recognize specific protocols like ISO 27001. Contact us if you want to try a demo, a free version of these tools, or whether you’re looking for professional advisory. At GB Advisors, we attempt to help you build your information security framework at all costs.



