The pandemic has challenged every industry. Its economic implications forced business leaders to contemplate how to maintain productivity through remote working and managing multiple processes outside the office. In addition, the pressure of cyberculture has led companies to implement various connectivity methods to provide continuity to their business activities. Providing services through mobile platforms, creating applications and implementing various software. But this transition to the World Wide Web via smartphones has also brought with it new forms of cyber threats. Let’s learn about cyber-hygiene at work and how it can help us combat cyber threats in mobile applications.
The demands of cyberculture

Cyberculture has to do with the inclination of people today to conduct daily activities through digital means. As a result, companies of all kinds are under pressure to focus almost entirely on online service delivery. Whether through a mobile application, a specialized website or online customer service. So many branches are emerging because of cyberculture, so cyber threats are constantly changing to keep up with them. And IT managers must maintain proper digital security as hackers become more sophisticated.
What we will now call cyber-hygiene culture entails being able to keep up with the changing nature of cyber threats, while remaining responsive to the ongoing demands of cyberculture. Especially the demands that have to do with the delivery of services via mobile devices.
Today, there are more than 3.2 billion smartphone users worldwide. It is no wonder that mobile applications are booming. Application usage and smartphone penetration continue to grow at a steady pace. Moreover, mobile apps are expected to generate more than $935 billion in revenue by 2023.
So, in the cyber environment, we now face the combination of traditional software vulnerabilities with the additional information and services that can be accessed through mobile apps. All of this calls for a different approach to cybersecurity.
Cyber hygiene in the work environment
Many organizations have had to quickly switch to remote working modalities. Therefore, the use of mobile devices to complete business tasks is a constant. One of the most important points of cyber-hygiene at work is to understand that personal devices do not have the same levels of security as corporately managed devices, which opens up a new attack surface for cyber criminals.
It is vital that organizations keep up to date with the latest threats and can prepare to respond appropriately to protect their staff. Prevention remains the main tool in the fight against malicious code and information theft.
To reduce the risk of computer incidents on mobile devices, it is necessary to build a secure work environment and educate yourself on best practices for the use of smartphones, the Internet, and technology in general. Here are some important points to take into account to combat cyber-threats in mobile applications at work:
-Authentication and sectorization:
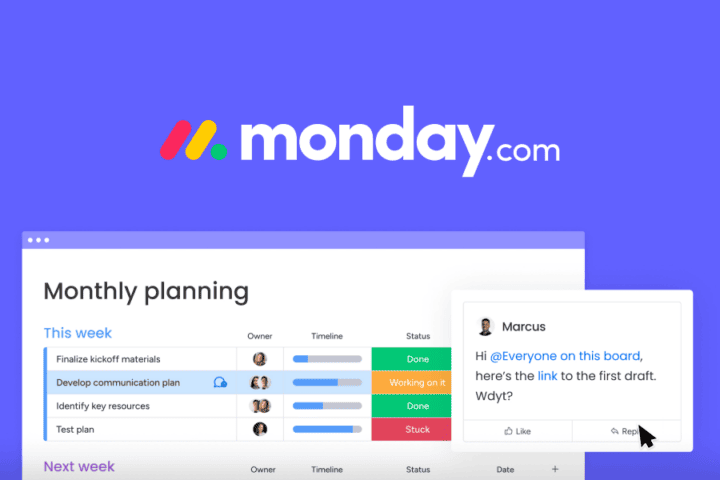
Not all employees need to have access to all sectors of the enterprise network. Nor is it necessary to know the access credits. If a web application contains different access points, then it is advisable that these are reserved for the various work areas. For example, there are companies that offer sectorized software for work areas: CRM, HR management, customer service, or IT management. And all of them have a specific mobile application.
Secure user authentication and authorization is also necessary. It is crucial to recognize the fact that a user can be a risk factor. Running the application could prevent access by hackers and malware, or the opposite.
The user’s authentication settings should include all the essential privacy points. As well as identity, session management and other mobile security features. You should include two-factor authentication (2FA) as well as multi-factor authentication (MFA) to enforce user authentication.
-Security training:
Investing in cybersecurity training helps organizations efficiently manage any risks. Employees could pose a huge risk to cyber-hygiene at work, even unintentionally. So knowing how to use the devices or knowing the security and data protection policies could make a significant difference.
An important cyber hygiene practice is the generation of secure passwords. It is recommended that employees do not use passwords that contain easily decipherable words or characters, such as personal names or sequences of numbers. If a mobile application is breached with a predictable password, all sensitive information is at risk.
-Use trusted devices:
The type of device used can also determine the online security of apps. In the cases of iOS and Android, both operating systems behave differently. That is why it is necessary to have different approaches for each operating system to ensure adequate security. Developers should be aware of the fact that data accumulated on any device is capable of causing a security breach.
It is advisable to always update the operating system and apps on devices to the latest available version. As well as backing up all the data on the computer, or at least the most valuable ones.
Managing vulnerabilities in mobile applications
Personal, financial and other data stored on mobile devices make mobile apps a lucrative target for cyberattacks. Therefore, the best cyber-hygiene practice for any enterprise is to make sure to vet apps before installation. Continually scanning installed apps for new vulnerabilities.

As with traditional desktop and enterprise applications, mobile apps can present security vulnerabilities. Attackers could exploit such vulnerabilities to access sensitive information and resources. It is therefore necessary to have automated, standardized and cost-effective methods and tools for developing, assessing, deploying and managing mobile applications.
Managing vulnerabilities entails addressing a new approach to testing the security of mobile applications with a critical eye. Seeking to continuously monitor the security posture of installed applications, identify malware and vulnerable code, and anticipate and react to future threats and vulnerabilities.
Having a routine cyber-hygiene procedure for your mobile apps and other software is beneficial for 3 distinct reasons: maintenance, security and trust. For employees and customers alike. Such a routine procedure is made possible by tools like AT&T cybersecurity that can assess critical infrastructures in web and mobile applications. Providing continuous validation and protection against cyber-threats, achieving security integration throughout the lifecycle of mobile applications.
If you want to know more about AT&T cybersecurity and how it can help you have a better cyber-hygiene at work and manage your mobile applications securely, contact us!