WE CONNECT PEOPLE, TECHNOLOGIES, AND PROCESSES
Our software and consulting services integrate people, technologies, and processes to achieve operational excellence and a smooth transition to digital transformation. You will gain an efficient, agile, and productive environment with our help.
WE CONNECT PEOPLE, TECHNOLOGIES, AND PROCESSES

Our software and consulting services integrate people, technologies, and processes to achieve operational excellence and a smooth transition to digital transformation. You will gain an efficient, agile, and productive environment with our help.
Get our best Webinars
and Demos for free!
Register and receive in your email the recordings
of our events on ITSM solutions, Help Desk, CRM, and more.

GET THE RIGHT SOFTWARE, ADAPT IT TO YOUR BUSINESS MODEL AND GO AS FAR AS YOU WANT
Are you looking for a tool that helps you streamline your IT Operations management and bring down IT costs? Check out our catalogue and choose the one that suits your needs.
Best advisory.
Best Team
We have certified professionals
ready to help you.
Best advisory.
Best Team
We have certified professionals
ready to help you.
GET EXPERT ADVICE
ON EVERY STEP YOU TAKE
Integrating new technologies within the company can be a great challenge. Luckily, you can count on our team of professionals to advise you on this:
- Choosing the tool that best suits your needs and type of industry
- Implementing your software within your systems
- Migrating your data safely
- Customizing your tool to meet your business objectives.



CEMENT YOUR PATH TO
DIGITAL TRANSFORMATION
Deliver more value to customers through the right tools. With our solutions you can:
- Provide better service to your customers: Through personalized experiences that meet their needs
- Increase your productivity: By automating and transforming your operational processes
- Make better decisions: Thanks to risk analysis based on useful data
KEEP YOUR BUSINESS SAFER FROM CYBER-THREATS
Attacks are on the rise and to stay one step ahead of threats you need smarter solutions. We have all kinds of tools for you to use:
- Get a complete view of your cyber exposure
- Prevent attacks through behavioral analysis
- Keep your passwords safe
- Ensure compliance with data protection regulations


SOME CYBERSECURITY FACTS

On average it is the
annual cost of losses
by cyberattacks

On average is the cost
annual by implementation
of tools and solutions
On average it is the
annual cost of losses
by cyberattacks


GET MORE INFORMATION ABOUT OUR PRODUCTS AND SERVICES
At GB Advisors we offer you a great variety of products and services aimed at satisfying different needs of your company. Check out our catalogue and discover everything we can do for you and your organization
TAKE ADVANTAGE OF ALL
THE BENEFITS OF REMOTE SUPPORT
What better way to take advantage of your tool than counting on a team that is always available? Our remote support service offers you:
- Prompt attention to your requests
- Expert advice
- Data privacy
- Real-time interaction with knowledge transfer

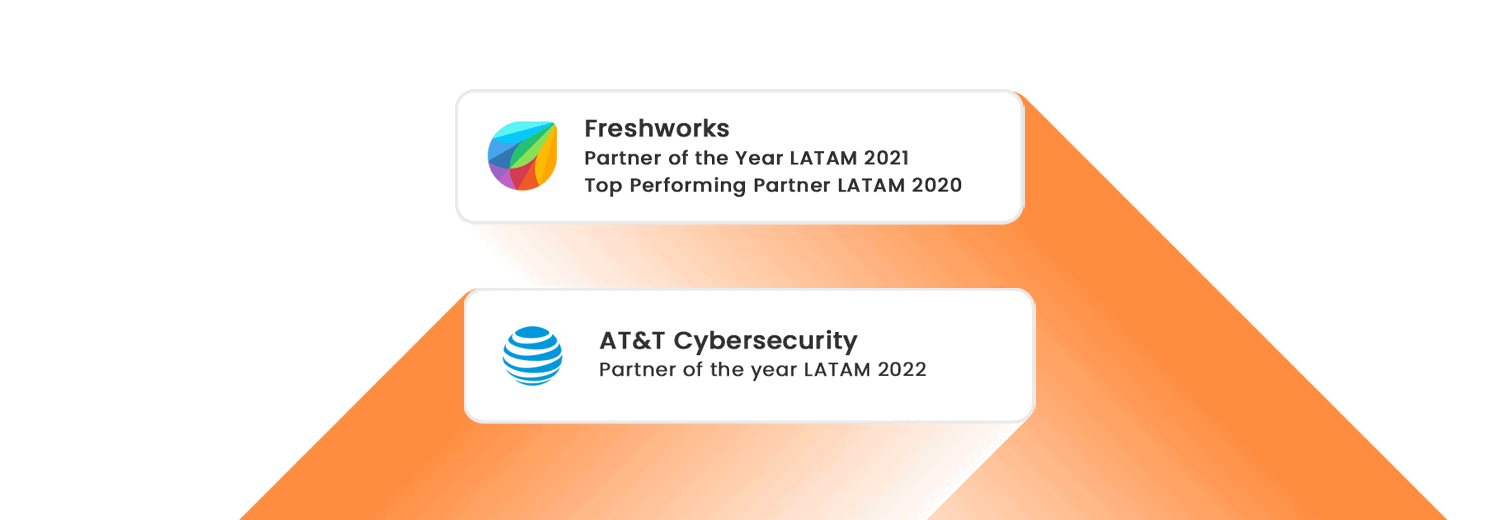
OUR PARTNERS

![]()
![]()

TECHNOLOGY BLOG

GET A QUOTE
AT NO COST
Do you want more information about our prices? Contact Us. Our team of professionals will be in charge of evaluating your request to offer you the best solutions adapted to your budget, always, guaranteeing the highest level of transparency. Ask all the questions you need, we are at your disposal to answer them.

Hundred customers business in more than 30 countries trust GB Advisors for your requirements of IT software and services

GB Advisors is growing on double digits year with strong financial results

100% Commitment, Ideas, Experience and Knowledge practical are the main factors that characterize us

With dozens of allies strategic we have demonstrated be at the forefront in enterprise Solutions